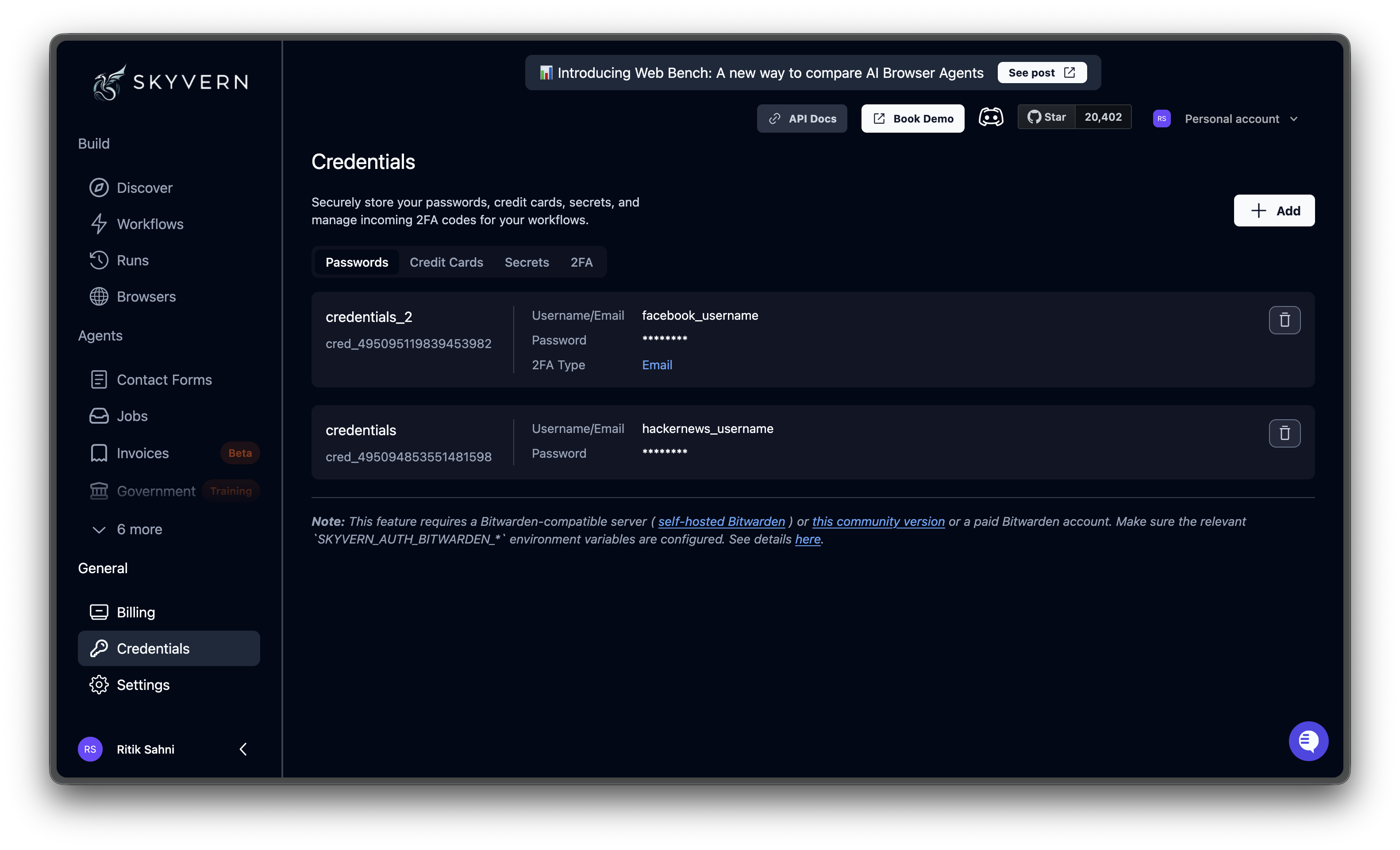
How Skyvern keeps credentials secure
Sensitive credential data never reaches the LLM, logs, or API responses.Encrypted at rest
When you save a credential, the sensitive data (passwords, card numbers, CVVs, and TOTP secrets) is sent to a secure vault that provides encryption at rest. Skyvern supports multiple vault backends: Bitwarden, 1Password, Azure Key Vault, and custom webhook providers. Skyvern’s own database stores only non-sensitive metadata: credential name, username, card last four digits, card brand, TOTP method, and similar identifiers. Passwords, full card numbers, CVVs, and TOTP secrets are stored exclusively in the vault.
Placeholders during execution
When a workflow runs, the LLM receives only placeholder IDs like
placeholder_Xk9m_password. The AI decides where to type on the page, but never sees the real values. No third party, including the LLM provider, ever accesses your actual credentials.Just-in-time injection
At the browser level, the automation layer resolves placeholders to real values and types them directly into the page. After execution, credential values that appear in HTTP Request block responses, block context snapshots, and conditional evaluation outputs are automatically masked before storage.
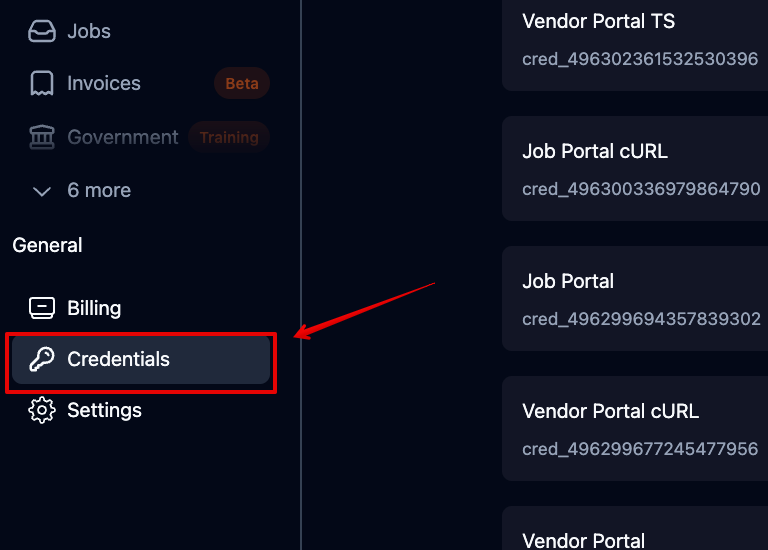
Quick start
What you can store
Password Credentials
Username, password, and optional 2FA configuration for automated logins
Credit Card Credentials
Payment card details for purchase and checkout workflows
Secret Credentials
A single sensitive string such as an API key, bearer token, or any value you don’t want hardcoded
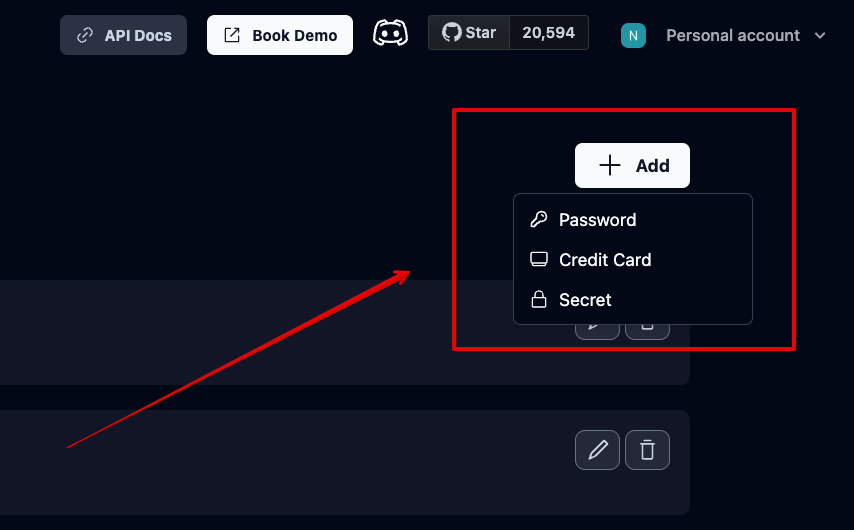
Secret credentials
Secrets store a single sensitive value (an API key, bearer token, or similar). Create one from + Add → Secret, give it a name and value, then reference it in HTTP Request, Code, or Workflow Trigger blocks using the credential parameter’s key:parameter_key with the key assigned to the credential parameter in the workflow editor (e.g., credentials, credentials_1).
Using credentials in workflows
The most common pattern is a Login block. A Login block is a workflow step that signs into a website using stored credentials. Select a credential from the dropdown, and Skyvern fills in the username, password, and 2FA code (if configured) automatically. See Block Reference for details. For workflows that need different credentials at runtime, add a Credential parameter (type:credential_id). When someone runs the workflow, they pick which credential to use from a dropdown. See Workflow Parameters for setup.
Deleting credentials
Click the trash icon on any credential row. Deletion is permanent and cannot be undone. If a workflow references a deleted credential, the run will fail during initialization until you assign a replacement.Password Credentials
Store logins with optional 2FA
Credit Card Credentials
Store payment details for checkout workflows
2FA / TOTP Setup
Configure and manage two-factor authentication
External Providers
Connect Bitwarden, 1Password, Azure Key Vault, or a custom API